Why Data Governance and Business Process Management Must Be Linked

Data governance and business process management must be linked.
Following the boom in data-driven business data governance (DG) has taken the modern enterprise by storm, garnering the attention of both the business and technical realms with an explosion of methodologies, targeted systems and training courses. That’s because a major gap needs to be addressed.
But despite all the admonitions and cautionary tales, little attention has focused on what can literally make or break any data governance initiative, turning it from a springboard for competitive advantage to a recipe for waste, anger and ultimately failure. The two key pivot points on which success hinges are business process management (BPM) and enterprise architecture. This article focuses on the critical connections between data governance and business process management.
Data Governance preparedness
This white paper explores the importance of data literacy and intelligence and how the right data governance platform, including a modern data catalog, is essential to organization in preparing for and recovering from a crisis.
Request White Paper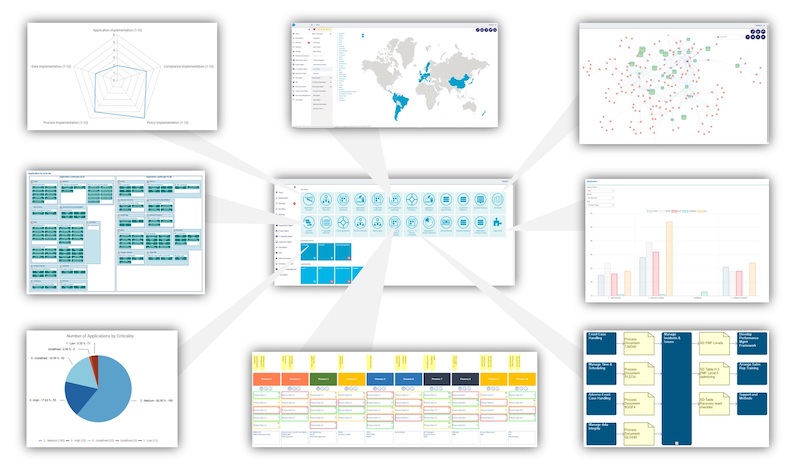
Based on a True Story: Data Governance Without Process Is Not Data Governance
The following is based on a true story about a global pharmaceutical company implementing a cloud-based, enterprise-wide CRM system with a third-party provider.
Given the system’s nature, the data it would process, and the scope of the deployment, data security and governance was front and center. There were countless meetings – some with more than 50 participants – with protocols sent, reviewed, adjusted and so on. In fact, more than half a dozen outside security companies and advisors (and yes, data governance experts) came in to help design the perfect data protection system around which the CRM system would be implemented.
The framework was truly mind-boggling: hundreds of security measures, dozens of different file management protocols, data security software appearing every step of the way. Looking at it as an external observer, it appeared to be an ironclad net of absolute safety and effective governance.
But as the CRM implementation progressed, holes began to appear. They were small at first but quickly grew to the size of trucks, effectively rendering months of preparatory work pointless.
Detailed data transfer protocols were subverted daily by consultants and company employees who thought speed was more important than safety. Software locks and systems were overridden with passwords freely communicated through emails and even written on Post-It Notes. And a two-factor authentication principle was reduced to one person entering half a password, with a piece of paper taped over half the computer screen, while another person entered the other half of the password before a third person read the entire password and pressed enter.
While these examples of security holes might seem funny – in a sad way – when you read them here, they represent a $500,000 failure that potentially could lead to a multi-billion-dollar security breach.
Why? Because there were no simple, effective and clearly defined processes to govern the immense investment in security protocols and software to ensure employees would follow them and management could audit and control them. Furthermore, the organization failed to realize how complex this implementation was and that process changes would be paramount.
Both such failures could have been avoided if the organization had a simple system of managing, adjusting and monitoring its processes. More to the point, the implementation of the entire security and governance framework would have cost less and been completed in half the time. Furthermore, if a failure or breach were discovered, it would be easy to trace and correct.
Data Governance Starts with BPM
In a rush to implement a data governance methodology and system, you can forget that a system must serve a process – and be governed/controlled by one.
To choose the correct system and implement it effectively and efficiently, you must know – in every detail – all the processes it will impact, how it will impact them, who needs to be involved and when. Do these questions sound familiar? They should because they are the same ones we ask in data governance. They involve impact analysis, ownership and accountability, control and traceability – all of which effectively documented and managed business processes enable.
Data sets are not important in and of themselves. Data sets become important in terms of how they are used, who uses them and what their use is – and all this information is described in the processes that generate, manipulate and use them. So, unless we know what those processes are, how can any data governance implementation be complete or successful?
Consider this scenario: We’ve perfectly captured our data lineage, so we know what our data sets mean, how they’re connected, and who’s responsible for them – not a simple task but a massive win for any organization. Now a breach occurs. Will any of the above information tell us why it happened? Or where? No! It will tell us what else is affected and who can manage the data layer(s), but unless we find and address the process failure that led to the breach, it is guaranteed to happen again.
By knowing where data is used – the processes that use and manage it – we can quickly, even instantly, identify where a failure occurs. Starting with data lineage (meaning our forensic analysis starts from our data governance system), we can identify the source and destination processes and the associated impacts throughout the organization. We can know which processes need to change and how. We can anticipate the pending disruptions to our operations and, more to the point, the costs involved in mitigating and/or addressing them.
But knowing all the above requires that our processes – our essential and operational business architecture – be accurately captured and modelled. Instituting data governance without processes is like building a castle on sand.
Rethinking Business Process Management
Modern organizations need a simple and easy-to-use BPM system with easy access to all the operational layers across the organization – from high-level business architecture all the way down to data. Sure, most organizations already have various solutions here and there, some with claims of being able to provide a comprehensive picture. But chances are they don’t, so you probably need to rethink your approach.
Modern BPM ecosystems are flexible, adjustable, easy-to-use and can support multiple layers simultaneously, allowing users to start in their comfort zones and mature as they work toward the organization’s goals.
Processes need to be open and shared in a concise, consistent way so all parts of the organization can investigate, ask questions, and then add their feedback and information layers. In other words, processes need to be alive and central to the organization because only then will the use of data and data governance be truly effective.
Are you willing to think outside the traditional boxes or silos that your organization’s processes and data live in?
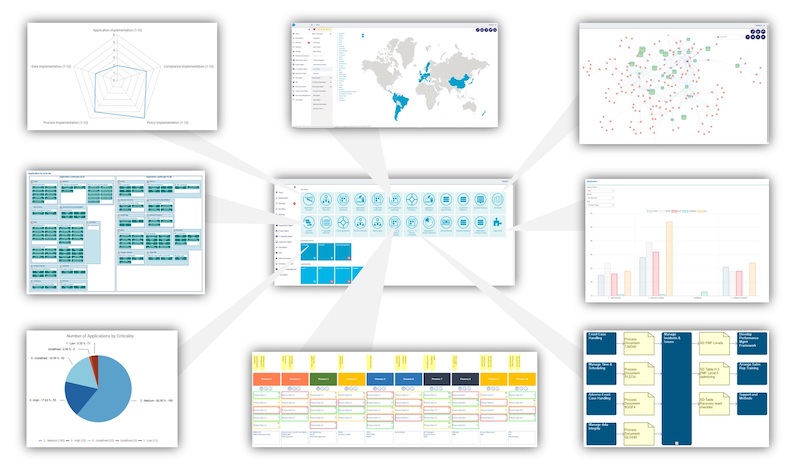
The erwin EDGE is one of the most comprehensive software platforms for managing an organization’s data governance and business process initiatives, as well as the whole data architecture. It allows natural, organic growth throughout the organization and the assimilation of data governance and business process management under the same platform provides a unique data governance experience because of its integrated, collaborative approach.
To learn more about erwin EDGE, and how data governance underpins and ensures data quality throughout the wider data management-suite, download our resource: Data Governance Is Everyone’s Business.
Data Governance is everyone's business.
Bringing IT and Business together for a new era in data driven enterprise.
Request White Paper